Your Phone Was There. Now You're a Suspect.
The Supreme Court is deciding whether police can demand Google's data on every device in a crime scene radius — without naming a single suspect. The Fourth Amendment has never been tested like this.
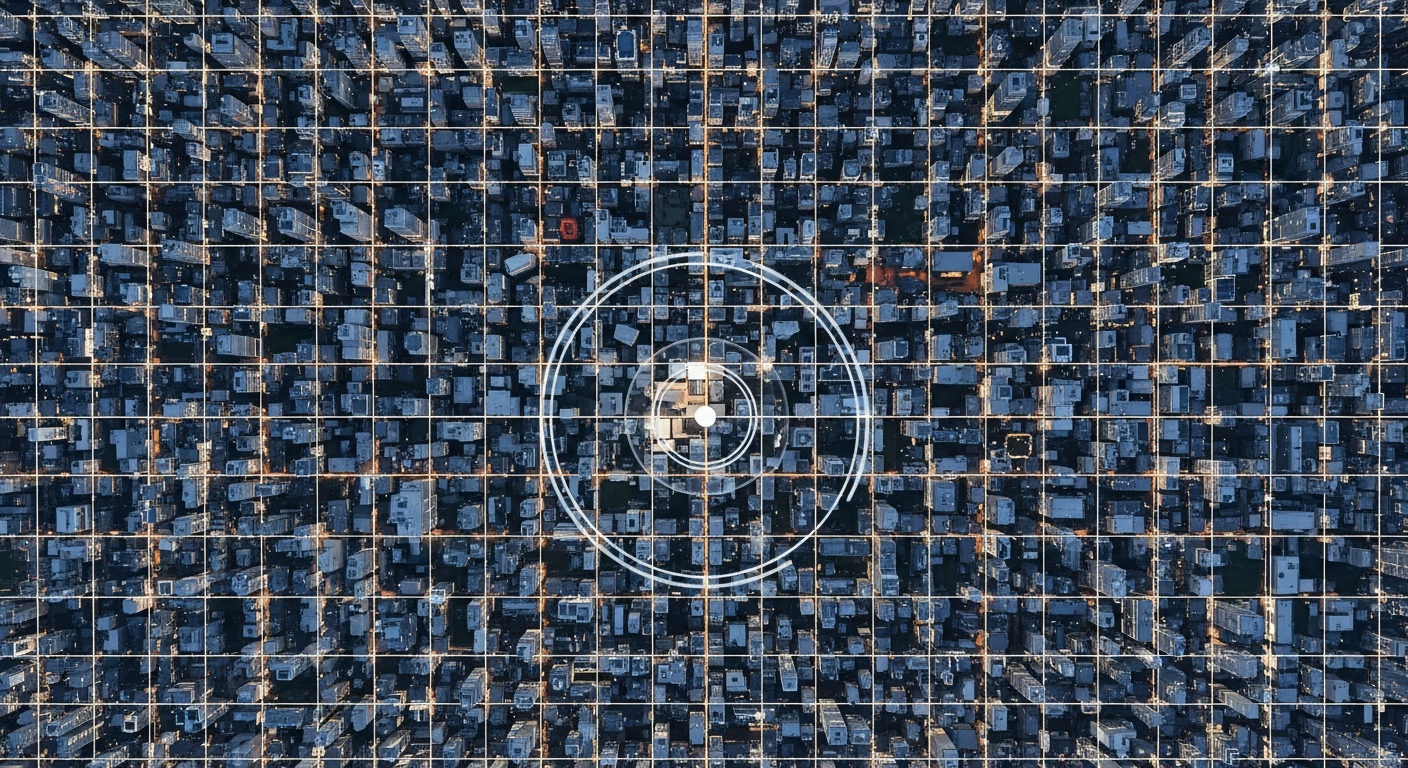
Your phone knows where you've been. Law enforcement knows that your phone knows. The question now before the Supreme Court is whether the government can demand that data from Google, not for a specific suspect, but for every device that passed through a given location at a given time.
That's a geofence warrant. And it may be the most consequential Fourth Amendment case of the smartphone era.
What a Geofence Warrant Actually Does
The mechanics are straightforward and unsettling. When investigators believe a crime occurred at a specific place and time, they serve Google (or Apple, or any location-data holder) with a warrant demanding a list of every device in that area. Google's Location History database, which stores GPS, Wi-Fi, and cell tower data for hundreds of millions of users, becomes an investigative dragnet.
The process runs in three steps. First, police request anonymized device IDs for everyone in a defined geographic radius during a defined time window. Second, investigators narrow that list and request identifying information on specific devices. Third, they identify the account holder and seek a full warrant for their data.
Innocent people have been misidentified and investigated, in some cases arrested, because their phones happened to ping a cell tower near a crime scene. One documented case involved a delivery driver who was briefly treated as a murder suspect because his route took him past the location at the wrong time.
The Circuit Split That Forced SCOTUS's Hand
Federal appeals courts have split sharply on whether geofence warrants violate the Fourth Amendment.
The Fourth Circuit, covering Virginia and the Carolinas, ruled in United States v. Chatrie that geofence warrants can be constitutional when properly scoped. It applied the "third-party doctrine," which holds that information voluntarily shared with a company carries no reasonable expectation of privacy.
The Fifth Circuit disagreed. It found that the scale and indiscriminate nature of geofence demands makes them categorically different from traditional targeted warrants, and potentially unconstitutional as general warrants, the exact type of search the Fourth Amendment was written to prohibit.
With circuits in direct conflict, the Supreme Court had little choice but to take it up.
Where the Left and Right Agree, and Where They Split
This is one of the rare cases where the usual political fault lines don't hold.
The civil liberties left, the ACLU, EFF, and privacy advocates, opposes geofence warrants on Fourth Amendment grounds. Mass collection of location data from innocent bystanders is a general warrant by another name, they argue. The Founders banned those explicitly because British soldiers used them to conduct sweeping searches without individual suspicion.
The libertarian right agrees. Organizations like the Cato Institute and conservative lawyers in the originalist tradition see geofence warrants as a clear Fourth Amendment violation, a digital-age end-run around the particularity requirement that warrants must name specific people and things to be seized. Justices Alito and Thomas have both signaled skepticism of expansive government surveillance powers in prior opinions.
The split comes with law enforcement. National security conservatives argue that geofence warrants have solved serious crimes, including bank robberies and the January 6th Capitol investigation, where Google's data helped identify dozens of participants. Restricting them removes a legitimate tool that operates within existing legal frameworks, they contend.
Both the Biden and Trump DOJs defended geofence warrant authority in litigation. That prosecutorial consensus across administrations is worth noting.
The Third-Party Doctrine Meets the Smartphone Age
At the core of this debate is a legal doctrine under serious strain: the idea that information you share with a third party, a bank, a phone company, now Google, loses Fourth Amendment protection entirely.
The Supreme Court took a significant step in Carpenter v. United States (2018), holding that long-term cell-site location data requires a warrant. Chief Justice Roberts, writing for a 5-4 majority, acknowledged the doctrine needed updating for the digital era: "A person does not surrender all Fourth Amendment protection by venturing into the public sphere."
Carpenter didn't resolve geofence warrants directly. Its logic points somewhere, though. When location tracking is comprehensive, persistent, and conducted without any individual suspicion, the traditional third-party doctrine doesn't hold.
The question is whether this Court follows that logic to its conclusion, or carves out a law enforcement exception wide enough to swallow the rule.
What a Ruling Could Mean
A ruling against geofence warrants would force police to identify suspects before seeking location data, the way traditional warrants work. It wouldn't prohibit all location-based investigation. It would require individual probable cause before sweeping up thousands of innocent people's data.
A ruling upholding geofence warrants would ratify a surveillance architecture most Americans don't know exists. A system where storing your location history with a tech company means law enforcement can, under the right conditions, make you a person of interest based on geography alone.
The consequences stretch well beyond criminal investigation. The same geofence architecture used to identify bank robbery suspects was used to identify abortion clinic visitors in states where that data became legally relevant after Dobbs. Data brokers sold that same location history to political campaigns. Whatever legal framework the Court sets here won't stay contained to one context.
The Question the Court Has to Answer
Does the Fourth Amendment protect you from being swept into a criminal investigation because your phone was in the wrong place at the wrong time?
The Founders had a word for searches that gathered information on the innocent in hopes of finding the guilty. They called them general warrants. They banned them.
The technology has changed. The principle hasn't.
Frequently Asked Questions
What is a geofence warrant?
A geofence warrant is a court order requiring a tech company, typically Google, to hand over data on every device present within a defined geographic area during a specific time window. Unlike a traditional warrant, it doesn't name a suspect. It sweeps up data on everyone in the area and works backward to identify persons of interest.
Are geofence warrants constitutional?
That's currently unsettled. The Fourth and Fifth Circuits have issued conflicting rulings, which is why the Supreme Court took up the issue. The central question is whether collecting location data on thousands of people without individual probable cause violates the Fourth Amendment's protection against unreasonable searches.
Has the Supreme Court addressed location tracking before?
Yes. In Carpenter v. United States (2018), the Court held 5-4 that long-term cell-site location data requires a warrant. The geofence case asks whether that same logic covers mass, undifferentiated location data collection.
Who opposes geofence warrants?
An unusual coalition: the civil liberties left (ACLU, EFF) and the libertarian right (Cato Institute, originalist legal scholars). Both argue that sweeping up data on innocent bystanders violates Fourth Amendment principles against general warrants.
Who supports geofence warrants?
Law enforcement and national security advocates argue the data has solved serious crimes and operates within existing legal frameworks. Both the Biden and Trump administrations defended their use in federal litigation.
Could a ruling affect more than criminal cases?
Yes. The same legal architecture governs how location data is accessed in abortion-related investigations after Dobbs, political surveillance, and commercial data broker sales. Whatever the Court decides applies across all of those contexts.